API. From 2G to 5G.
SilentAuth+
The silent network authentication API is built on GSMA TS.43 entitlement framework, leveraging EAP-AKA SIM-based authentication. It authenticates users via SIM cryptographic credentials, invisibly, in milliseconds, on any network from 2G to 5G, with a unique USSD fallback for markets where data does not reach.
P2A Authentication
.png)
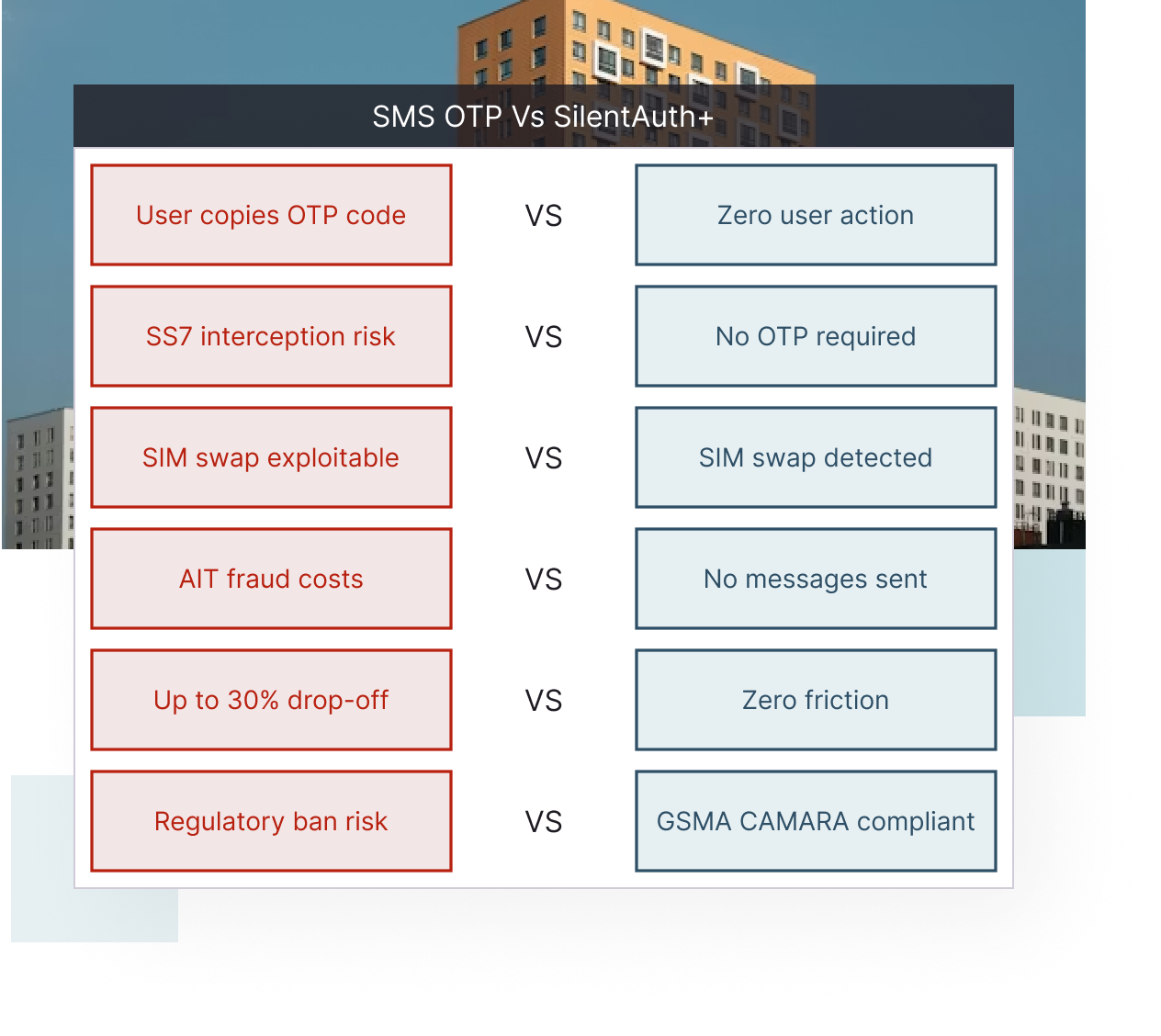
Regulatory bans are now active across APAC and MENA. Malaysia, Hong Kong and Singapore have restricted SMS OTP for financial services. SilentAuth+ replaces it entirely




IPification relies on IP-address matching, which requires mobile data and does not work on Wi-Fi or 2G/3G. Shush is designed for mature 4G/5G markets. Neither covers the full 2G-to-5G and Wi-Fi range with USSD fallback that SilentAuth+ delivers.
How can telcos monetise authentication APIs?
Telcos can monetise authentication by exposing network-based identity APIs to enterprises, generating revenue from user verification instead of relying on declining SMS OTP traffic. This creates a new high-margin API revenue stream.
What is TS.43 authentication and why does it matter for operators?
TS.43 is a GSMA standard that enables SIM-based authentication using EAP-AKA across mobile and Wi-Fi networks. It allows operators to act as trusted identity providers instead of relying on third-party authentication methods.
How does silent authentication help telcos reclaim authentication from OTT players?
Silent authentication shifts identity verification from apps and SMS OTP back into the mobile network. This allows telcos to control authentication flows and capture value from every login and transaction.
What is Number Verify 2 (NV2) and how is it used by telcos?
Number Verify 2 is a GSMA Open Gateway API that confirms a phone number matches the active SIM card. Telcos can offer NV2 as a standardised API for real-time identity verification.
How does network-based authentication compare to SMS OTP?
Network-based authentication is faster, more secure, and does not require user input. Unlike SMS OTP, it is resistant to SIM swap fraud, phishing, and delivery failures.
Can telco authentication work across 2G, 3G, 4G, and 5G networks?
Yes, network-based authentication can work across all generations of mobile networks using a combination of TS.43, USSD fallback, and operator integrations.
How does authentication API revenue compare to SMS OTP revenue?
Authentication APIs provide scalable, usage-based revenue with higher margins, while SMS OTP revenues are declining due to fraud, regulation, and user friction.
What role do telcos play in digital identity and GSMA Open Gateway?
Telcos are positioned to become global identity providers through GSMA Open Gateway APIs like Number Verify. They can offer secure, interoperable identity services to enterprises worldwide.

.png)